Spring Security 3.0���ݿ̬ʵ��Ȩ����
��һ�νӴ�Spring Security�����������˺ܶ����ϣ��м�ʾ���ģ����ǰ��û�����Ȩ����Ϣ������XML���棬�����ֲ�̫�ʺ�һ�����Ŀ����Щ�����Ƿ���Դ���뽲������������������Լ��乤��ԭ����������Ŀʱ�������������е��ҿ���Щ���ϵ�ʱ�����Ǻܴ�æ�����������������ϡ���Ϳ����������ң����ĵ�ϣ���и����ʽ��е�Ԫ���������ߣ������һ�����ȡ�����������"Ԫ��������ô����"�����쾲������֮ǰ������Щ��ϸ���˿������о��������Ҳ������ô��ô����ץ��
�������� SpringIDE 3.0��Spring Security 3.0.2��myibatis��Maven��MySql
��ǰ���spring�����Լ�Maven�����ܰ���myibatis�����þͲ�˵��
���ȣ�
1����Ҫ������Ҫ��JAR����pom������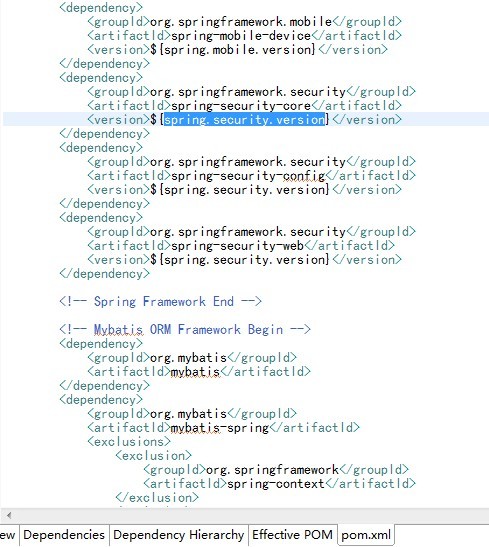
2����web.xml������spring security������
<filter><filter-name>springSecurityFilterChain</filter-name><filter-class>org.springframework.web.filter.DelegatingFilterProxy</filter-class></filter><filter-mapping><filter-name>springSecurityFilterChain</filter-name><url-pattern>/*</url-pattern></filter-mapping>
<?xml version="1.0" encoding="UTF-8"?><b:beans xmlns="http://www.springframework.org/schema/security" xmlns:b="http://www.springframework.org/schema/beans" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:schemaLocation="http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans-3.0.xsd http://www.springframework.org/schema/security http://www.springframework.org/schema/security/spring-security-3.0.xsd"><!-- <global-method-security pre-post-annotations="enabled" /> --><!-- access-denied-page���÷���ʧ��ҳ�� --><http auto-config="true" access-denied-page="/accessDenied.htm"><!-- ��Ҫ����ͼƬ�Ⱦ�̬��Դ������**�������Կ�ԽĿ¼��*�����Կ�ԽĿ¼�� --> <intercept-url pattern="/**/*.jpg" filters="none" /> <intercept-url pattern="/**/*.png" filters="none" /> <intercept-url pattern="/**/*.gif" filters="none" /> <intercept-url pattern="/**/*.css" filters="none" /> <intercept-url pattern="/**/*.js" filters="none" /> <intercept-url pattern="/login.htm*" filters="none"/> <!-- <intercept-url pattern="/index.htm" access="ROLE_USER,ROLE_ADMIN"/> <intercept-url pattern="/header.htm" access="ROLE_USER,ROLE_ADMIN"/> <intercept-url pattern="/left.htm" access="ROLE_USER,ROLE_ADMIN"/> --> <intercept-url pattern="/**" access="ROLE_USER"/><!-- ���õ�¼ҳ�� --><form-login login-page="/login.htm"default-target-url="/" authentication-failure-url="/login.htm?error=true"login-processing-url="/springSecurityLogin"/><!--"��ס��"���ܣ����ó־û�����(���û��ĵ�¼��Ϣ��������ݿ����) --><!-- <remember-me/> --><!-- �û��˳�����תҳ�� --><logout logout-success-url="/login.htm" invalidate-session="true" logout-url="/logout" /><!-- �Ự��������������¼�쳣��error-if-maximum-exceeded = falseΪ�ڶ��ε�¼�ͻ�ʹǰһ����¼ʧЧ --> <session-management invalid-session-url="/error/errorPage.jsp"><concurrency-control max-sessions="1" error-if-maximum-exceeded="false" /></session-management><!--�����Զ���Ĺ����� ����FILTER_SECURITY_INTERCEPTOR֮ǰ��Ч --><custom-filter ref="customFilterSecurityInterceptor" before="FILTER_SECURITY_INTERCEPTOR" /></http><!-- ������֤������ --><authentication-manager alias="authenticationManager"><authentication-provider user-service-ref="customUserDetailsService"> <password-encoder hash="md5"/><!-- <jdbc-user-service data-source-ref="dataSource"/> --></authentication-provider></authentication-manager></b:beans>
package com.doone.wisdom.security.impl;import java.util.ArrayList;import java.util.Collection;import java.util.List;import javax.annotation.Resource;import org.springframework.security.core.GrantedAuthority;import org.springframework.security.core.authority.GrantedAuthorityImpl;import org.springframework.security.core.userdetails.User;import org.springframework.security.core.userdetails.UserDetails;import org.springframework.security.core.userdetails.UsernameNotFoundException;import org.springframework.stereotype.Service;import com.doone.wisdom.dao.security.UserDao;import com.doone.wisdom.entity.security.RoleEntity;import com.doone.wisdom.entity.security.UserEntity;import com.doone.wisdom.security.service.CustomUserDetailsService;/** * TODO(������һ�仰����������ְ��). * @ClassName: CustomUserDetailsServiceImpl * @author Johnny_L_Q */@Service("customUserDetailsService")public class CustomUserDetailsServiceImpl implements CustomUserDetailsService { /** * @Fields serialVersionUID : TODO����һ�仰�������������ʾʲô��. */ private static final long serialVersionUID = 1L; @Resource private UserDao userDao; /* * �����û����ж��Ƿ���� * <p>Title: loadUserByUsername</p> * <p>Description: </p> * @param arg0 * @return * @throws UsernameNotFoundException * @see org.springframework.security.core.userdetails.UserDetailsService#loadUserByUsername(java.lang.String) */ @Override public UserDetails loadUserByUsername(String username) throws UsernameNotFoundException { UserEntity user = userDao.getUser(username); if (null == user) { throw new UsernameNotFoundException("�û�" + username + "������"); } Collection<GrantedAuthority> auths = new ArrayList<GrantedAuthority>(); List<String> list = userDao.getAuthoritiesByUsername(username); for (int i = 0; i < list.size(); i++) { auths.add(new GrantedAuthorityImpl(list.get(i))); System.out.println("loadUserByUsername : " + list.get(i)); } //��ΪUserEntityʵ����UserDetails������Ҳ����ֱ�ӷ���user return new User(username, user.getPassword(), true, true, true, true, auths); }}package com.doone.wisdom.security.impl;import java.util.Collection;import java.util.Iterator;import org.springframework.security.access.AccessDeniedException;import org.springframework.security.access.ConfigAttribute;import org.springframework.security.access.SecurityConfig;import org.springframework.security.authentication.InsufficientAuthenticationException;import org.springframework.security.core.Authentication;import org.springframework.security.core.GrantedAuthority;import org.springframework.security.core.userdetails.jdbc.JdbcDaoImpl;import org.springframework.security.provisioning.JdbcUserDetailsManager;import org.springframework.stereotype.Service;import com.doone.wisdom.security.service.CustomAccessDecisionManager;/** * * AccessdecisionManager��Spring security���Ǻ���Ҫ�ġ� * * ����֤���ּ�������ˣ����е�Authenticationʵ����Ҫ������һ��GrantedAuthority���������С� ����Ǹ���������Ȩ�ޡ� * GrantedAuthority����ͨ��AuthenticationManager ���浽 * Authentication�����Ȼ���AccessDecisionManager��������������Ȩ�жϡ� * * Spring Security�ṩ��һЩ�������������ƶ�ȫ����ķ���Ȩ�ޣ����緽�����û�web���� * һ���Ƿ�����ִ�е��õ�Ԥ���þ���������AccessDecisionManagerʵ�ֵġ� ��� AccessDecisionManager * ��AbstractSecurityInterceptor���ã� �����������շ��ʿ��Ƶľ����� * ���AccessDecisionManager�ӿڰ������������� * * void decide(Authentication authentication, Object secureObject, * List<ConfigAttributeDefinition> config) throws AccessDeniedException; boolean * supports(ConfigAttribute attribute); boolean supports(Class clazz); * * �ӵ�һ���������Կ�������AccessDecisionManagerʹ�÷�����������������Ϣ�����������֤����ʱ���о����� * �ر��ǣ�����ʵ�İ�ȫ�����������õ�ʱ���ݰ�ȫObject������Щ������ ���磬�����Ǽ��谲ȫ������һ��MethodInvocation�� * ������Ϊ�κ�Customer������ѯMethodInvocation�� * Ȼ����AccessDecisionManager��ʵ��һЩ����İ�ȫ������ȷ�������Ƿ��������Ǹ��ͻ��ϲ����� * ������ʱ��ܾ���ʵ�ֽ��׳�һ��AccessDeniedException�쳣�� * * ��� supports(ConfigAttribute) ������������ʱ�� * AbstractSecurityInterceptor���ã�������AccessDecisionManager * �Ƿ����ִ�д���ConfigAttribute�� supports(Class)��������ȫ������ʵ�ֵ��ã� * ������ȫ����������ʾ��AccessDecisionManager֧�ְ�ȫ��������͡� * TODO(������һ�仰����������ְ��). * @ClassName: CustomAccessDecisionManagerImpl * @author Johnny_L_Q */@Service("customAccessDecisionManager")public class CustomAccessDecisionManagerImpl implements CustomAccessDecisionManager { /* * <p>Title: decide</p> * <p>Description: </p> * @param arg0 * @param arg1 * @param arg2 * @throws AccessDeniedException * @throws InsufficientAuthenticationException * @see org.springframework.security.access.AccessDecisionManager * #decide(org.springframework.security.core.Authentication, java.lang.Object, java.util.Collection) */ @Override public void decide(Authentication authentication, Object object, Collection<ConfigAttribute> configAttributes) throws AccessDeniedException, InsufficientAuthenticationException { if (null == configAttributes) { return; } Iterator<ConfigAttribute> cons = configAttributes.iterator(); while(cons.hasNext()){ ConfigAttribute ca = cons.next(); String needRole = ((SecurityConfig) ca).getAttribute(); //gra Ϊ�û����������Ȩ�ޣ�needRoleΪ������Ӧ����ԴӦ���е�Ȩ�� for (GrantedAuthority gra : authentication.getAuthorities()) { if (needRole.trim().equals(gra.getAuthority().trim())) { return; } } } throw new AccessDeniedException("Access Denied"); } /* * <p>Title: supports</p> * <p>Description: </p> * @param arg0 * @return * @see org.springframework.security.access.AccessDecisionManager#supports(org.springframework.security.access.ConfigAttribute) */ @Override public boolean supports(ConfigAttribute arg0) { // TODO Auto-generated method stub return true; } /* * <p>Title: supports</p> * <p>Description: </p> * @param arg0 * @return * @see org.springframework.security.access.AccessDecisionManager#supports(java.lang.Class) */ @Override public boolean supports(Class<?> arg0) { // TODO Auto-generated method stub return true; }}package com.doone.wisdom.security.impl;import java.io.IOException;import javax.annotation.Resource;import javax.servlet.FilterChain;import javax.servlet.FilterConfig;import javax.servlet.ServletException;import javax.servlet.ServletRequest;import javax.servlet.ServletResponse;import org.springframework.beans.factory.annotation.Qualifier;import org.springframework.security.access.AccessDecisionManager;import org.springframework.security.access.SecurityMetadataSource;import org.springframework.security.access.intercept.AbstractSecurityInterceptor;import org.springframework.security.access.intercept.InterceptorStatusToken;import org.springframework.security.authentication.AuthenticationManager;import org.springframework.security.web.FilterInvocation;import org.springframework.security.web.access.intercept.FilterInvocationSecurityMetadataSource;import org.springframework.stereotype.Service;import com.doone.wisdom.security.service.CustomFilterSecurityInterceptor;/** * �ù���������Ҫ���þ���ͨ��spring������IoC����securityMetadataSource�� * securityMetadataSource�൱�ڱ������Զ����CostomInvocationSecurityMetadataSourceService�� * ��CostomInvocationSecurityMetadataSourceService������������ݿ���ȡȨ����Դ��װ�䵽HashMap�У� * ��Spring Securityʹ�ã�����Ȩ��У�顣 * * TODO(������һ�仰����������ְ��). * @ClassName: CustomFilterSecurityInterceptorImpl * @author Johnny_L_Q */@Service("customFilterSecurityInterceptor")public class CustomFilterSecurityInterceptorImpl extends AbstractSecurityInterceptor implements CustomFilterSecurityInterceptor { @Resource @Qualifier("customInvocationSecurityMetadataSource") private FilterInvocationSecurityMetadataSource securityMetadataSource; @Resource @Qualifier("customAccessDecisionManager") @Override public void setAccessDecisionManager( AccessDecisionManager accessDecisionManager) { // TODO Auto-generated method stub super.setAccessDecisionManager(accessDecisionManager); }/* @Resource @Qualifier("customAccessDecisionManager") public AccessDecisionManager accessDecisionManager;*/ /* @Resource @Qualifier("authenticationManager") public AuthenticationManager authenticationManager;*/ @Resource @Qualifier("authenticationManager") @Override public void setAuthenticationManager(AuthenticationManager newManager) { super.setAuthenticationManager(newManager); } /* * <p>Title: doFilter</p> * <p>Description: </p> * @param arg0 * @param arg1 * @param arg2 * @throws IOException * @throws ServletException * @see javax.servlet.Filter#doFilter(javax.servlet.ServletRequest, javax.servlet.ServletResponse, javax.servlet.FilterChain) */ @Override public void doFilter(ServletRequest request, ServletResponse response, FilterChain chain) throws IOException, ServletException { FilterInvocation fi = new FilterInvocation(request, response, chain); infoke(fi); } /** * TODO(������һ�仰�����������������). * @param fi * @throws ServletException * @throws IOException */ private void infoke(FilterInvocation fi) throws IOException, ServletException { InterceptorStatusToken token = super.beforeInvocation(fi); try { fi.getChain().doFilter(fi.getRequest(), fi.getResponse()); } finally { super.afterInvocation(token, null); } } /* * <p>Title: init</p> * <p>Description: </p> * @param arg0 * @throws ServletException * @see javax.servlet.Filter#init(javax.servlet.FilterConfig) */ @Override public void init(FilterConfig arg0) throws ServletException { // TODO Auto-generated method stub } /* * <p>Title: getSecureObjectClass</p> * <p>Description: </p> * @return * @see org.springframework.security.access.intercept.AbstractSecurityInterceptor#getSecureObjectClass() */ @Override public Class<?> getSecureObjectClass() { // TODO Auto-generated method stub return FilterInvocation.class; } /* * <p>Title: obtainSecurityMetadataSource</p> * <p>Description: </p> * @return * @see org.springframework.security.access.intercept.AbstractSecurityInterceptor#obtainSecurityMetadataSource() */ @Override public SecurityMetadataSource obtainSecurityMetadataSource() { // TODO Auto-generated method stub return this.securityMetadataSource; } /* * <p>Title: destroy</p> * <p>Description: </p> * @see javax.servlet.Filter#destroy() */ @Override public void destroy() { // TODO Auto-generated method stub } public FilterInvocationSecurityMetadataSource getSecurityMetadataSource() { return securityMetadataSource; } public void setSecurityMetadataSource( FilterInvocationSecurityMetadataSource securityMetadataSource) { this.securityMetadataSource = securityMetadataSource; }}package com.doone.wisdom.security.impl;import java.util.ArrayList;import java.util.Collection;import java.util.HashMap;import java.util.Iterator;import java.util.List;import javax.annotation.PostConstruct;import javax.annotation.Resource;import org.springframework.security.access.ConfigAttribute;import org.springframework.security.access.SecurityConfig;import org.springframework.security.web.FilterInvocation;import org.springframework.security.web.util.AntUrlPathMatcher;import org.springframework.security.web.util.UrlMatcher;import org.springframework.stereotype.Service;import com.doone.wisdom.entity.security.AuthorityEntity;import com.doone.wisdom.entity.security.RoleEntity;import com.doone.wisdom.security.service.CustomInvocationSecurityMetadataSource;import com.doone.wisdom.service.iface.AuthorityService;import com.doone.wisdom.service.iface.ResourceService;/** * TODO(������һ�仰����������ְ��). * @ClassName: CustomInvocationSecurityMetadataSourceImpl * @author Johnny_L_Q */@Service("customInvocationSecurityMetadataSource")public class CustomInvocationSecurityMetadataSourceImpl implements CustomInvocationSecurityMetadataSource { @Resource private ResourceService resourceService; @Resource private AuthorityService authorityService; private UrlMatcher urlMatcher = new AntUrlPathMatcher(); //private AntPathRequestMatcher pathMatcher; private HashMap<String, Collection<ConfigAttribute>> resourceMap = null; /** * * �Զ��巽�����������뵽Spring������ * ָ��initΪ��ʼ�������������ݿ��ж�ȡ��Դ * TODO(������һ�仰�����������������). */ @PostConstruct public void init() { loadResourceDefine(); } /** * * TODO(����������ʱ��ͼ���������Դ��Ϣ). */ private void loadResourceDefine() { // ��Web����������ʱ����ȡϵͳ�е�����Ȩ�ޡ� //sql = "select authority_name from pub_authorities"; List<AuthorityEntity> query = authorityService.getAllAuthoritys(); /**//* * Ӧ������ԴΪkey�� Ȩ��Ϊvalue�� ��Դͨ��Ϊurl�� Ȩ������Щ��ROLE_Ϊǰ�Ľ�ɫ�� һ����Դ�����ɶ��Ȩ�������ʡ� * sparta */ resourceMap = new HashMap<String, Collection<ConfigAttribute>>(); for (AuthorityEntity auth : query) { String authName = auth.getAuthorityName(); ConfigAttribute ca = new SecurityConfig(auth.getAuthorityName()); List<String> resources = resourceService.getResourcesByAuthName(authName); for (String str : resources) { //String authName = auth2.getAuthorityName(); String url = str; /**//* * �ж���Դ�ļ���Ȩ�Ķ�Ӧ��ϵ������Ѿ�������ص���Դurl����Ҫͨ����urlΪkey��ȡ��Ȩ���ϣ���Ȩ�����ӵ�Ȩ�����С� * sparta */ if (resourceMap.containsKey(url)) { Collection<ConfigAttribute> value = resourceMap.get(url); value.add(ca); resourceMap.put(url, value); } else { Collection<ConfigAttribute> atts = new ArrayList<ConfigAttribute>(); atts.add(ca); resourceMap.put(url, atts); } } } } /** * TODO(�Զ��巽������List<Role>����ת��Ϊ�����Ҫ��Collection<ConfigAttribute>����). * @param roles ��ɫ���� * @return list ��װ�õ�Collection���� */ private Collection<ConfigAttribute> listToCollection(List<RoleEntity> roles) { List<ConfigAttribute> list = new ArrayList<ConfigAttribute>(); for (RoleEntity role : roles) { list.add(new SecurityConfig(role.getRoleName())); } return list; } /* * <p>Title: getAllConfigAttributes</p> * <p>Description: </p> * @return * @see org.springframework.security.access.SecurityMetadataSource#getAllConfigAttributes() */ @Override public Collection<ConfigAttribute> getAllConfigAttributes() { return null; } /* * <p>Title: getAttributes</p> * <p>Description: </p> * @param arg0 * @return * @throws IllegalArgumentException * @see org.springframework.security.access.SecurityMetadataSource#getAttributes(java.lang.Object) */ @Override public Collection<ConfigAttribute> getAttributes(Object object) throws IllegalArgumentException { //object ��һ��URL ,Ϊ�û�����URL String url = ((FilterInvocation)object).getRequestUrl(); if("/".equals(url)){ return null; } int firstQuestionMarkIndex = url.indexOf("."); //�ж������Ƿ���в��� ����в�����ȥ������ĺ��Ͳ���(/index.do --> /index) if(firstQuestionMarkIndex != -1){ url = url.substring(0,firstQuestionMarkIndex); } Iterator<String> ite = resourceMap.keySet().iterator(); //ȡ�������URL��������ȡ��������Դ���Ƚ� while (ite.hasNext()) { String resURL = ite.next(); if(urlMatcher.pathMatchesUrl(url, resURL)){ return resourceMap.get(resURL); } } return null; } /* * <p>Title: supports</p> * <p>Description: </p> * @param arg0 * @return * @see org.springframework.security.access.SecurityMetadataSource#supports(java.lang.Class) */ @Override public boolean supports(Class<?> arg0) { // TODO Auto-generated method stub return true; }}/*MySQL Data TransferSource Host: localhostSource Database: wisdomTarget Host: localhostTarget Database: wisdomDate: 2012/10/19 9:29:52*/SET FOREIGN_KEY_CHECKS=0;-- ------------------------------ Table structure for pub_authorities-- ----------------------------CREATE TABLE `pub_authorities` ( `authority_id` varchar(32) COLLATE utf8_bin NOT NULL, `authority_name` varchar(40) COLLATE utf8_bin NOT NULL, `authority_desc` varchar(100) COLLATE utf8_bin DEFAULT NULL, `enabled` int(10) NOT NULL, `issys` int(10) NOT NULL, PRIMARY KEY (`authority_id`)) ENGINE=InnoDB DEFAULT CHARSET=utf8 COLLATE=utf8_bin;-- ------------------------------ Records -- ----------------------------INSERT INTO `pub_authorities` VALUES ('1', 'ROLE_ADMIN', '��ҳ���������', '1', '0');INSERT INTO `pub_authorities` VALUES ('2', 'ROLE_USER', '��ҳ', '1', '0');/*MySQL Data TransferSource Host: localhostSource Database: wisdomTarget Host: localhostTarget Database: wisdomDate: 2012/10/19 9:30:25*/SET FOREIGN_KEY_CHECKS=0;-- ------------------------------ Table structure for pub_resources-- ----------------------------CREATE TABLE `pub_resources` ( `resource_id` varchar(32) COLLATE utf8_bin NOT NULL, `resource_name` varchar(100) COLLATE utf8_bin NOT NULL, `resource_type` varchar(40) COLLATE utf8_bin NOT NULL, `priority` int(10) NOT NULL, `resource_string` varchar(200) COLLATE utf8_bin NOT NULL, `resource_desc` varchar(100) COLLATE utf8_bin DEFAULT NULL, `enabled` int(10) NOT NULL, `issys` int(10) NOT NULL, PRIMARY KEY (`resource_id`)) ENGINE=InnoDB DEFAULT CHARSET=utf8 COLLATE=utf8_bin;-- ------------------------------ Records -- ----------------------------INSERT INTO `pub_resources` VALUES ('1', '��ҳ���������', 'action', '0', '/funcPages/adManager', '��ҳ���������', '1', '0');INSERT INTO `pub_resources` VALUES ('2', '��ҳ', 'action', '0', '/index', '��ҳ', '1', '0');/*MySQL Data TransferSource Host: localhostSource Database: wisdomTarget Host: localhostTarget Database: wisdomDate: 2012/10/19 9:30:17*/SET FOREIGN_KEY_CHECKS=0;-- ------------------------------ Table structure for pub_authorities_resources-- ----------------------------CREATE TABLE `pub_authorities_resources` ( `id` varchar(32) COLLATE utf8_bin NOT NULL, `authority_id` varchar(32) COLLATE utf8_bin NOT NULL, `resource_id` varchar(32) COLLATE utf8_bin NOT NULL, PRIMARY KEY (`id`), KEY `fk_res_aut` (`authority_id`), KEY `fk_res` (`resource_id`), CONSTRAINT `fk_res` FOREIGN KEY (`resource_id`) REFERENCES `pub_resources` (`resource_id`), CONSTRAINT `fk_res_aut` FOREIGN KEY (`authority_id`) REFERENCES `pub_authorities` (`authority_id`)) ENGINE=InnoDB DEFAULT CHARSET=utf8 COLLATE=utf8_bin;-- ------------------------------ Records -- ----------------------------INSERT INTO `pub_authorities_resources` VALUES ('1', '1', '1');INSERT INTO `pub_authorities_resources` VALUES ('2', '2', '2');/*MySQL Data TransferSource Host: localhostSource Database: wisdomTarget Host: localhostTarget Database: wisdomDate: 2012/10/19 9:30:30*/SET FOREIGN_KEY_CHECKS=0;-- ------------------------------ Table structure for pub_roles-- ----------------------------CREATE TABLE `pub_roles` ( `role_id` varchar(32) COLLATE utf8_bin NOT NULL, `role_name` varchar(100) COLLATE utf8_bin NOT NULL, `role_desc` varchar(100) COLLATE utf8_bin DEFAULT NULL, `enabled` int(10) NOT NULL, `issys` int(10) NOT NULL COMMENT '��ɫ��', PRIMARY KEY (`role_id`)) ENGINE=InnoDB DEFAULT CHARSET=utf8 COLLATE=utf8_bin;-- ------------------------------ Records -- ----------------------------INSERT INTO `pub_roles` VALUES ('1', 'ROLE_ADMIN', 'ϵͳ��¼', '1', '0');INSERT INTO `pub_roles` VALUES ('2', 'ROLE_USER', '��ͨ�û�', '1', '0');/*MySQL Data TransferSource Host: localhostSource Database: wisdomTarget Host: localhostTarget Database: wisdomDate: 2012/10/19 9:30:36*/SET FOREIGN_KEY_CHECKS=0;-- ------------------------------ Table structure for pub_roles_authorities-- ----------------------------CREATE TABLE `pub_roles_authorities` ( `id` varchar(32) COLLATE utf8_bin NOT NULL, `role_id` varchar(32) COLLATE utf8_bin NOT NULL, `authority_id` varchar(32) COLLATE utf8_bin NOT NULL, PRIMARY KEY (`id`), KEY `fk_aut_role` (`role_id`), KEY `fk_aut` (`authority_id`), CONSTRAINT `fk_aut` FOREIGN KEY (`authority_id`) REFERENCES `pub_authorities` (`authority_id`), CONSTRAINT `fk_aut_role` FOREIGN KEY (`role_id`) REFERENCES `pub_roles` (`role_id`)) ENGINE=InnoDB DEFAULT CHARSET=utf8 COLLATE=utf8_bin;-- ------------------------------ Records -- ----------------------------INSERT INTO `pub_roles_authorities` VALUES ('1', '1', '1');INSERT INTO `pub_roles_authorities` VALUES ('2', '1', '2');INSERT INTO `pub_roles_authorities` VALUES ('3', '2', '2');/*MySQL Data TransferSource Host: localhostSource Database: wisdomTarget Host: localhostTarget Database: wisdomDate: 2012/10/19 9:30:42*/SET FOREIGN_KEY_CHECKS=0;-- ------------------------------ Table structure for pub_users-- ----------------------------CREATE TABLE `pub_users` ( `user_id` varchar(32) COLLATE utf8_bin NOT NULL, `user_account` varchar(30) COLLATE utf8_bin NOT NULL, `user_name` varchar(40) COLLATE utf8_bin NOT NULL, `user_password` varchar(100) COLLATE utf8_bin NOT NULL, `enabled` int(10) NOT NULL, `issys` int(10) NOT NULL, `user_desc` varchar(100) COLLATE utf8_bin DEFAULT NULL COMMENT '�û���', PRIMARY KEY (`user_id`)) ENGINE=InnoDB DEFAULT CHARSET=utf8 COLLATE=utf8_bin;-- ------------------------------ Records -- ----------------------------INSERT INTO `pub_users` VALUES ('1', 'admin', 'admin', '21232f297a57a5a743894a0e4a801fc3', '1', '1', '��������Ա');INSERT INTO `pub_users` VALUES ('2', 'user', 'user', 'ee11cbb19052e40b07aac0ca060c23ee', '1', '0', '��ͨ�û�');/*MySQL Data TransferSource Host: localhostSource Database: wisdomTarget Host: localhostTarget Database: wisdomDate: 2012/10/19 9:30:48*/SET FOREIGN_KEY_CHECKS=0;-- ------------------------------ Table structure for pub_users_roles-- ----------------------------CREATE TABLE `pub_users_roles` ( `id` varchar(32) CHARACTER SET utf8 NOT NULL, `user_id` varchar(32) COLLATE utf8_bin NOT NULL, `role_id` varchar(32) COLLATE utf8_bin NOT NULL COMMENT '��ɫ���û��м��', PRIMARY KEY (`id`), KEY `fk_user` (`user_id`), KEY `fk_role` (`role_id`), CONSTRAINT `fk_role` FOREIGN KEY (`role_id`) REFERENCES `pub_roles` (`role_id`), CONSTRAINT `fk_user` FOREIGN KEY (`user_id`) REFERENCES `pub_users` (`user_id`)) ENGINE=InnoDB DEFAULT CHARSET=utf8 COLLATE=utf8_bin;-- ------------------------------ Records -- ----------------------------INSERT INTO `pub_users_roles` VALUES ('1', '1', '1');INSERT INTO `pub_users_roles` VALUES ('2', '2', '2');select b.authority_name from PUB_ROLES a, PUB_AUTHORITIES b, PUB_ROLES_AUTHORITIES c where c.role_id = a.role_id and c.authority_id = b.authority_id and a.role_name in (select role_name from PUB_USERS_ROLES ur, PUB_USERS u, PUB_ROLES r where ur.user_id = u.user_id and ur.role_id = r.role_id and u.user_name = #{username} )select * from PUB_USERS u where u.user_name = #{username}select b.resource_string from PUB_AUTHORITIES_RESOURCES a ,PUB_RESOURCES b, PUB_AUTHORITIES c where a.resource_id = b.resource_id and a.authority_id = c.authority_id and c.authority_name = #{authName}select * from pub_authorities